What are Executables? | Binary Exploitation 0x00
#BinaryExploitation #ELF #Executables
This video is an introduction to ELF Executables in Linux. Also it's the first video of a new series called Binary Exploitation.
💬 Discord: https://discord.gg/6KKQHvgJwv
👨💻 HackerCamp: https://hackercamp.co
🐤 Twitter: https://twitter.com/PwnFunction
🎵 Track: Warriyo - Mortals (feat. Laura Brehm)
NCS link: https://www.youtube.com/watch?v=yJg-Y5byMMw
Видео What are Executables? | Binary Exploitation 0x00 канала PwnFunction
This video is an introduction to ELF Executables in Linux. Also it's the first video of a new series called Binary Exploitation.
💬 Discord: https://discord.gg/6KKQHvgJwv
👨💻 HackerCamp: https://hackercamp.co
🐤 Twitter: https://twitter.com/PwnFunction
🎵 Track: Warriyo - Mortals (feat. Laura Brehm)
NCS link: https://www.youtube.com/watch?v=yJg-Y5byMMw
Видео What are Executables? | Binary Exploitation 0x00 канала PwnFunction
Показать
Комментарии отсутствуют
Информация о видео
Другие видео канала
 0x00 To Hero - Learning Binary Exploitation Ep. 1
0x00 To Hero - Learning Binary Exploitation Ep. 1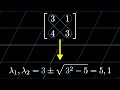 A quick trick for computing eigenvalues | Chapter 15, Essence of linear algebra
A quick trick for computing eigenvalues | Chapter 15, Essence of linear algebra Why some Functions are Dangerous | Binary Exploitation 0x01
Why some Functions are Dangerous | Binary Exploitation 0x01 Object Oriented Programming vs Functional Programming
Object Oriented Programming vs Functional Programming Simple Tools and Techniques for Reversing a binary - bin 0x06
Simple Tools and Techniques for Reversing a binary - bin 0x06![BASIC Buffer Overflow | Ryan's CTF [13] Everyday I'm Bufferin](https://i.ytimg.com/vi/YVlTDPhTA9U/default.jpg) BASIC Buffer Overflow | Ryan's CTF [13] Everyday I'm Bufferin
BASIC Buffer Overflow | Ryan's CTF [13] Everyday I'm Bufferin Cross-Site Scripting (XSS) Explained
Cross-Site Scripting (XSS) Explained CppCon 2018: Matt Godbolt “The Bits Between the Bits: How We Get to main()”
CppCon 2018: Matt Godbolt “The Bits Between the Bits: How We Get to main()” Can you fit a whole game into a QR code?
Can you fit a whole game into a QR code? XXE Challenge - Google CTF
XXE Challenge - Google CTF How the Apple AirTags were hacked
How the Apple AirTags were hacked Making an OS (x86) - CPU, Assembly, Booting
Making an OS (x86) - CPU, Assembly, Booting Why do programmers use hexadecimal numbers?
Why do programmers use hexadecimal numbers? Abusing iframes to Steal Cookies - Google CTF
Abusing iframes to Steal Cookies - Google CTF Insecure Deserialization Attack Explained
Insecure Deserialization Attack Explained Cross-Site Request Forgery (CSRF) Explained
Cross-Site Request Forgery (CSRF) Explained Why you should Close Your Files | Binary Exploitation 0x02
Why you should Close Your Files | Binary Exploitation 0x02 Coding Adventure: Chess AI
Coding Adventure: Chess AI how Hackers SNiFF (capture) network traffic // MiTM attack
how Hackers SNiFF (capture) network traffic // MiTM attack I Got Rejected from Y Combinator
I Got Rejected from Y Combinator