Elliptic Curves - Computerphile
Just what are elliptic curves and why use a graph shape in cryptography? Dr Mike Pound explains.
Mike's myriad Diffie-Hellman videos: https://www.youtube.com/playlist?list=PLzH6n4zXuckpoaxDKOOV26yhgoY2S-xYg
https://www.facebook.com/computerphile
https://twitter.com/computer_phile
This video was filmed and edited by Sean Riley.
Computer Science at the University of Nottingham: https://bit.ly/nottscomputer
Computerphile is a sister project to Brady Haran's Numberphile. More at http://www.bradyharan.com
Видео Elliptic Curves - Computerphile канала Computerphile
Mike's myriad Diffie-Hellman videos: https://www.youtube.com/playlist?list=PLzH6n4zXuckpoaxDKOOV26yhgoY2S-xYg
https://www.facebook.com/computerphile
https://twitter.com/computer_phile
This video was filmed and edited by Sean Riley.
Computer Science at the University of Nottingham: https://bit.ly/nottscomputer
Computerphile is a sister project to Brady Haran's Numberphile. More at http://www.bradyharan.com
Видео Elliptic Curves - Computerphile канала Computerphile
Показать
Комментарии отсутствуют
Информация о видео
Другие видео канала
 Elliptic Curve Back Door - Computerphile
Elliptic Curve Back Door - Computerphile Securing Stream Ciphers (HMAC) - Computerphile
Securing Stream Ciphers (HMAC) - Computerphile Wana Decrypt0r (Wanacry Ransomware) - Computerphile
Wana Decrypt0r (Wanacry Ransomware) - Computerphile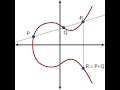 Elliptic Curve Diffie Hellman
Elliptic Curve Diffie Hellman Breaking ECDSA (Elliptic Curve Cryptography) - rhme2 Secure Filesystem v1.92r1 (crypto 150)
Breaking ECDSA (Elliptic Curve Cryptography) - rhme2 Secure Filesystem v1.92r1 (crypto 150)
 Is DeepFake Really All That? - Computerphile
Is DeepFake Really All That? - Computerphile Elliptic Curves and Modular Forms | The Proof of Fermat’s Last Theorem
Elliptic Curves and Modular Forms | The Proof of Fermat’s Last Theorem Secret Key Exchange (Diffie-Hellman) - Computerphile
Secret Key Exchange (Diffie-Hellman) - Computerphile Elliptic curves
Elliptic curves Key Exchange Problems - Computerphile
Key Exchange Problems - Computerphile Maze Solving - Computerphile
Maze Solving - Computerphile Elliptic Curve Cryptography Tutorial - Understanding ECC through the Diffie-Hellman Key Exchange
Elliptic Curve Cryptography Tutorial - Understanding ECC through the Diffie-Hellman Key Exchange Public Key Cryptography: RSA Encryption Algorithm
Public Key Cryptography: RSA Encryption Algorithm One Encryption Standard to Rule Them All! - Computerphile
One Encryption Standard to Rule Them All! - Computerphile Running an SQL Injection Attack - Computerphile
Running an SQL Injection Attack - Computerphile Diceware & Passwords - Computerphile
Diceware & Passwords - Computerphile What are Digital Signatures? - Computerphile
What are Digital Signatures? - Computerphile 2FA: Two Factor Authentication - Computerphile
2FA: Two Factor Authentication - Computerphile How did the NSA hack our emails?
How did the NSA hack our emails?