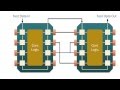
Remote Debugging ARM Chip with SWD/JTAG - Hardware Wallet Research #3
Using ARM SWD with a development board to debug the chip with GDB.
research: https://wallet.fail
DISCLAIMER: The security research shown here was done a while ago and since then the software and hardware was updated; These videos are not sponsored or endorsed by Ledger.
-=[ 💻 Related Products ]=-
→ Ledger Nano S:* https://amzn.to/2VAhMvM
→ USB Hub with switches:* https://amzn.to/2SJuaYv
→ any STM32 Nucleo-64 development board:* https://amzn.to/2VDDE9J
-=[ 🔴 Stuff I use ]=-
→ Microphone:* https://geni.us/ntg3b
→ Graphics tablet:* https://geni.us/wacom-intuos
→ Camera#1 for streaming:* https://geni.us/sony-camera
→ Lens for streaming:* https://geni.us/sony-lense
→ Connect Camera#1 to PC:* https://geni.us/cam-link
→ Keyboard:* https://geni.us/mech-keyboard
→ Old Microphone:* https://geni.us/mic-at2020usb
US Store Front:* https://www.amazon.com/shop/liveoverflow
-=[ ❤️ Support ]=-
→ per Video: https://www.patreon.com/join/liveoverflow
→ per Month: https://www.youtube.com/channel/UClcE-kVhqyiHCcjYwcpfj9w/join
-=[ 🐕 Social ]=-
→ Twitter: https://twitter.com/LiveOverflow/
→ Website: https://liveoverflow.com/
→ Subreddit: https://www.reddit.com/r/LiveOverflow/
→ Facebook: https://www.facebook.com/LiveOverflow/
-=[ 📄 P.S. ]=-
All links with "*" are affiliate links.
LiveOverflow / Security Flag GmbH is part of the Amazon Affiliate Partner Programm.
#HardwareSecurity #ReverseEngineering
Видео Remote Debugging ARM Chip with SWD/JTAG - Hardware Wallet Research #3 канала LiveOverflow
research: https://wallet.fail
DISCLAIMER: The security research shown here was done a while ago and since then the software and hardware was updated; These videos are not sponsored or endorsed by Ledger.
-=[ 💻 Related Products ]=-
→ Ledger Nano S:* https://amzn.to/2VAhMvM
→ USB Hub with switches:* https://amzn.to/2SJuaYv
→ any STM32 Nucleo-64 development board:* https://amzn.to/2VDDE9J
-=[ 🔴 Stuff I use ]=-
→ Microphone:* https://geni.us/ntg3b
→ Graphics tablet:* https://geni.us/wacom-intuos
→ Camera#1 for streaming:* https://geni.us/sony-camera
→ Lens for streaming:* https://geni.us/sony-lense
→ Connect Camera#1 to PC:* https://geni.us/cam-link
→ Keyboard:* https://geni.us/mech-keyboard
→ Old Microphone:* https://geni.us/mic-at2020usb
US Store Front:* https://www.amazon.com/shop/liveoverflow
-=[ ❤️ Support ]=-
→ per Video: https://www.patreon.com/join/liveoverflow
→ per Month: https://www.youtube.com/channel/UClcE-kVhqyiHCcjYwcpfj9w/join
-=[ 🐕 Social ]=-
→ Twitter: https://twitter.com/LiveOverflow/
→ Website: https://liveoverflow.com/
→ Subreddit: https://www.reddit.com/r/LiveOverflow/
→ Facebook: https://www.facebook.com/LiveOverflow/
-=[ 📄 P.S. ]=-
All links with "*" are affiliate links.
LiveOverflow / Security Flag GmbH is part of the Amazon Affiliate Partner Programm.
#HardwareSecurity #ReverseEngineering
Видео Remote Debugging ARM Chip with SWD/JTAG - Hardware Wallet Research #3 канала LiveOverflow
Показать
Комментарии отсутствуют
Информация о видео
Другие видео канала
 Setup and Find Entry-point in ARM Firmware - Hardware Wallet Research #4
Setup and Find Entry-point in ARM Firmware - Hardware Wallet Research #4 EEVblog #499 - What is JTAG and Boundary Scan?
EEVblog #499 - What is JTAG and Boundary Scan? Blue-pill STM32 Programming Using ST-LINK V2 Dongle
Blue-pill STM32 Programming Using ST-LINK V2 Dongle What do Nintendo Switch and iOS 9.3 have in common? CVE-2016-4657 walk-through
What do Nintendo Switch and iOS 9.3 have in common? CVE-2016-4657 walk-through
 JTAG TAP Controller Tutorial
JTAG TAP Controller Tutorial Breaking AES with ChipWhisperer - Piece of scake (Side Channel Analysis 100)
Breaking AES with ChipWhisperer - Piece of scake (Side Channel Analysis 100) Looking at the PCB & Chips - Hardware Wallet Research #2
Looking at the PCB & Chips - Hardware Wallet Research #2 Intro to Hardware Reversing: Finding a UART and getting a shell
Intro to Hardware Reversing: Finding a UART and getting a shell #274 Free Inline Debugging for ESP32 and Arduino Sketches
#274 Free Inline Debugging for ESP32 and Arduino Sketches Threat Models - Hardware Wallet Research #1
Threat Models - Hardware Wallet Research #1 #03 - How To Find The JTAG Interface - Hardware Hacking Tutorial
#03 - How To Find The JTAG Interface - Hardware Hacking Tutorial Analysing a Firefox Malware browserassist.dll - FLARE-On 2018
Analysing a Firefox Malware browserassist.dll - FLARE-On 2018 Don't Get Phished! (Phishing Awareness)
Don't Get Phished! (Phishing Awareness) Uploading Arduino bootloader on a new micro-controller // With J-Link SEGGER, SWD for MCU SAMD21G
Uploading Arduino bootloader on a new micro-controller // With J-Link SEGGER, SWD for MCU SAMD21G STM32 F103 BLUEPILL - Getting Started with Arduino Core
STM32 F103 BLUEPILL - Getting Started with Arduino Core Hardware Power Glitch Attack (Fault Injection) - rhme2 Fiesta (FI 100)
Hardware Power Glitch Attack (Fault Injection) - rhme2 Fiesta (FI 100) JTAG/Boundary Scan: Basics
JTAG/Boundary Scan: Basics Identify Bootloader main() and find Button Press Handler - Hardware Wallet Research #5
Identify Bootloader main() and find Button Press Handler - Hardware Wallet Research #5 9.2 - Debugging - GDB Tutorial
9.2 - Debugging - GDB Tutorial